In August 2016, 119,754 BTC was stolen from the Hong Kong cryptocurrency exchange Bitfinex. The funds moved through thousands of addresses over six years — mixers, chain hops, darknet markets. In February 2022, the FBI recovered 94,636 BTC in 133 minutes and swept everything into a single custody address. That address has not sent a single satoshi since.
This is a walkthrough of looking it up. The same address queried across four tools, with four different results. Then a trace on one transaction that pulls a thread from the seizure back to a staging address funded 13 days before the theft happened.
The address
The label “FBI 3” does not exist on the Bitcoin blockchain. It was assigned by blockchain intelligence firms tracking the seizure. The address itself is a string of characters with no name attached. The label lives in the analytical layer built on top of the protocol — and which tool you use determines whether you see it at all.
Four tools, four different experiences
| Tool | Data returned | Observer | Notes |
|---|---|---|---|
| Blockchair | Full data, heavy noise | Blockchair | Balance and history present. Page carries gambling ads and embedded commercial AML scoring. |
| 3xpl (clearnet) | Full data, clean | 3xpl | 175 transactions, live balance, USD value. No ads, no commercial overlays. |
| 3xpl (.onion) | Full data, clean | Nobody | Identical result via Tor hidden service. Query does not reach 3xpl servers. |
| blockchain.com API | Raw JSON, no auth | Blockchain.com | blockchain.info/rawaddr/[address] — complete data, no account required. 100 transactions per call. |
| WalletExplorer | Full data + clustering | Chainalysis | Wallet grouping, labelled addresses, CSV export. Creator now works at Chainalysis — stated on the site. |
Blockchair: data inside a commercial layer
Blockchair returns the address without issue. Balance, USD equivalent, full transaction history. The data is accurate.
What surrounds it requires attention. The page loads with gambling promotions alongside a “dApp Gallery” panel embedding commercial analytics products. A third-party AML risk score rates the address at 15 out of 100. Further widgets offer sanctions screening and paid wallet statement generation.
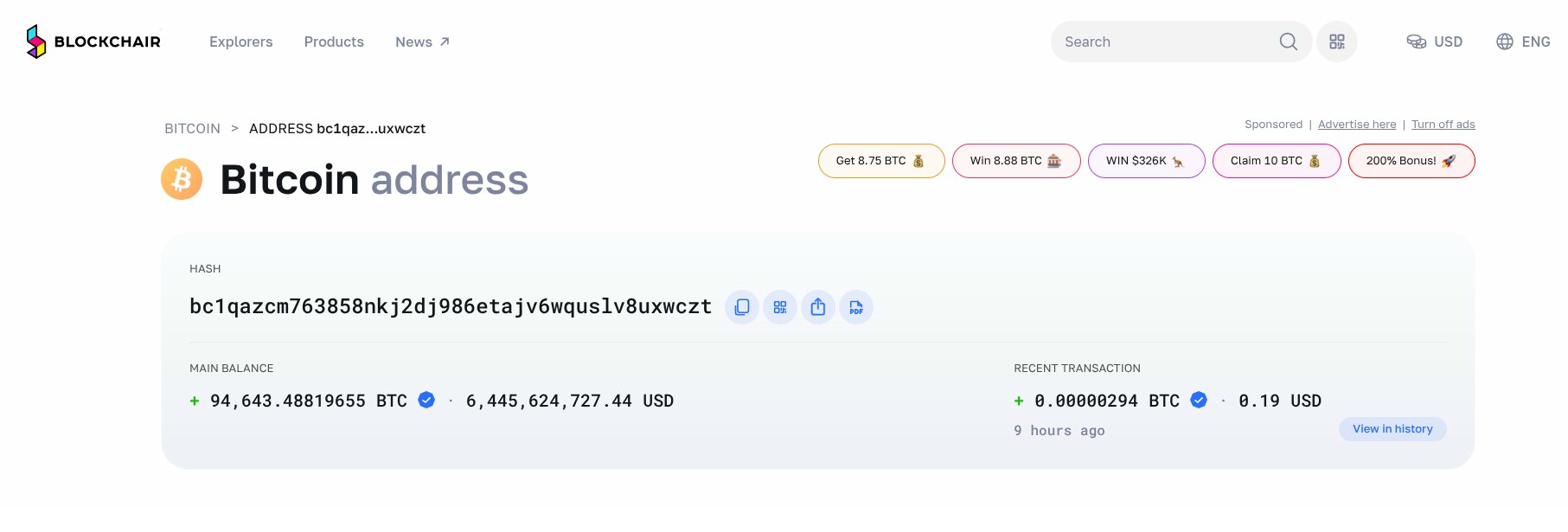
None of this invalidates the data. But the commercial layer shapes how a researcher reads a result, and the AML scores on that panel are not independent analysis — they are products from third-party vendors paying for placement.
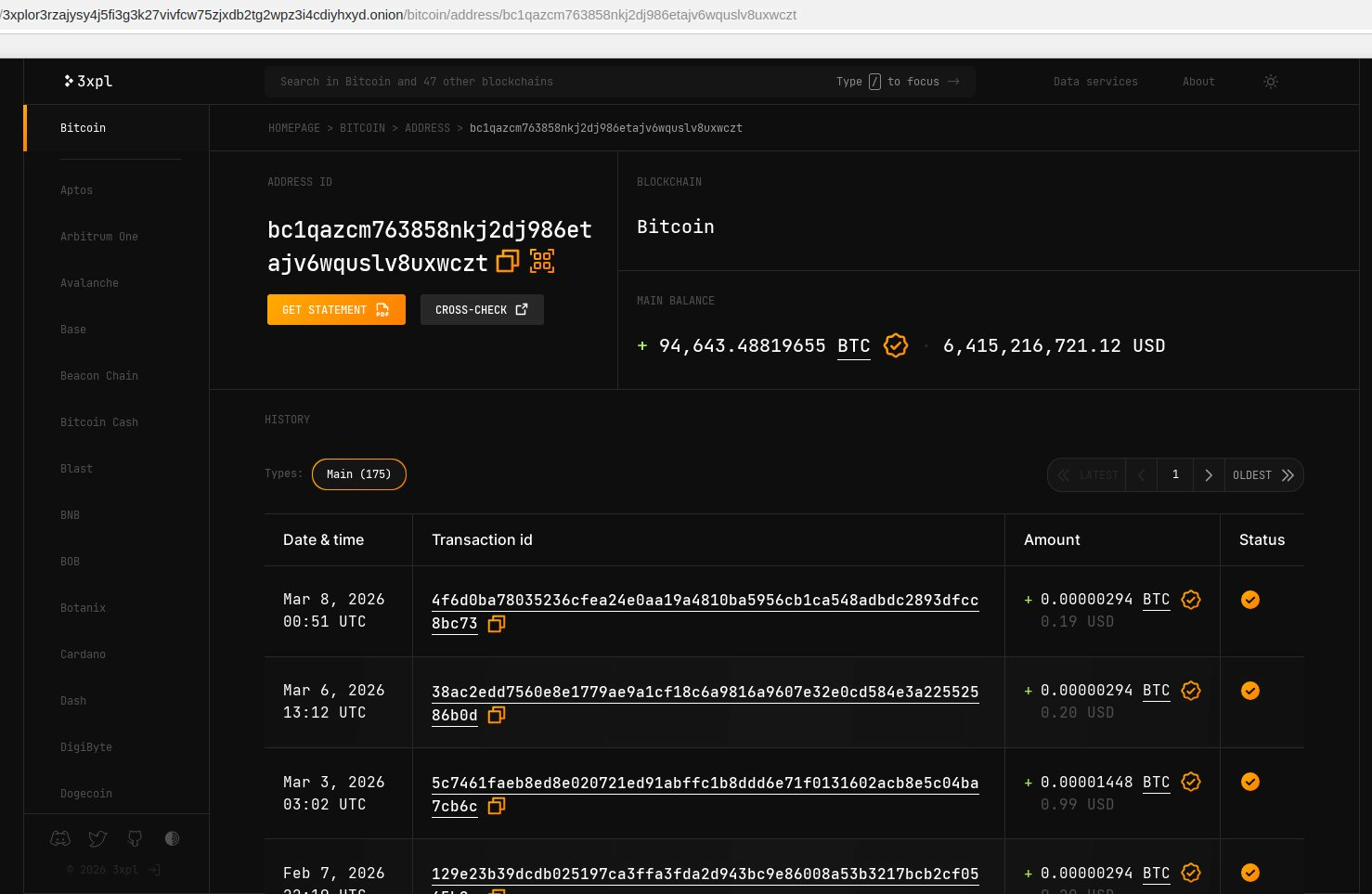
3xpl: the same data without the layer
3xpl was founded by former Blockchair developers. The editorial approach is similar; the commercial model is not. The address page loads cleanly: balance, transaction count, full history, USD value. No ads, no embedded third-party tools, no risk scoring.
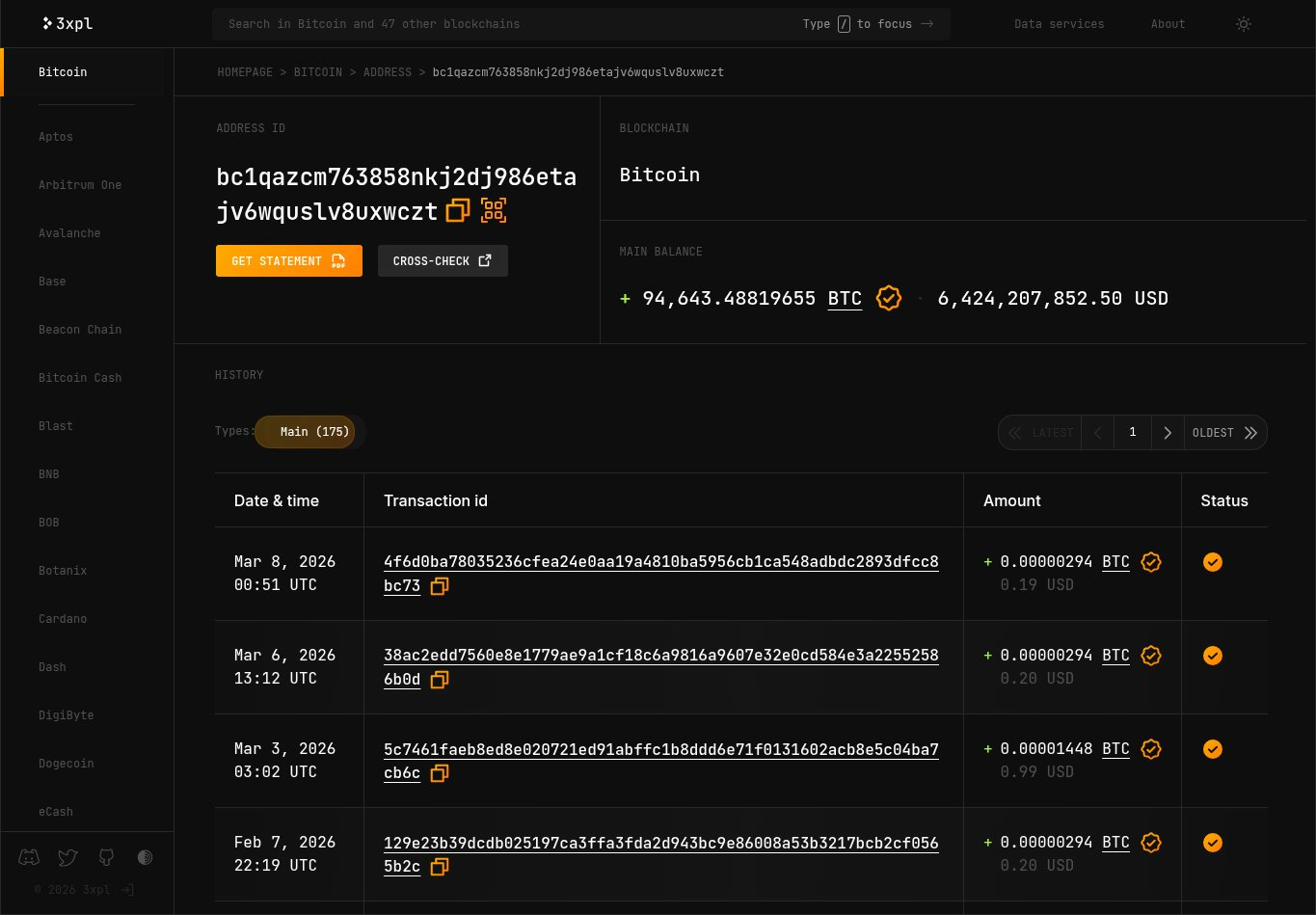
3xpl operates a Tor hidden service at 3xplor3rzajysy4j5fi3g3k27vivfcw75zjxdb2tg2wpz3i4cdiyhxyd.onion. The same address navigated to via that URL returns identical data. The operational difference is that the query terminates within the Tor network — 3xpl’s servers receive no IP, no timestamp, no log of the lookup.
The blockchain.com API
The blockchain.com website is friction-heavy by design. Sign-in prompts appear on address pages. Addresses truncate in the UI. Transaction lists paginate without obvious export paths.
The API behind it has none of these constraints. The endpoint https://blockchain.info/rawaddr/bc1qazcm763858nkj2dj986etajv6wquslv8uxwczt returns a complete JSON object with no authentication. Total received: 9,464,348,819,655 satoshis — 94,643.48819655 BTC. Total sent: 0. 174 transactions on record at time of query, 100 returned per call, the remainder retrieved with an offset parameter.
Most researchers using the browser interface do not know the API exists. The underlying data is identical. The access path is just not surfaced.
WalletExplorer: clustering and the Chainalysis connection
WalletExplorer groups addresses into wallets using co-spending heuristics — the principle that inputs appearing in the same transaction were likely controlled by the same entity. The FBI3 address belongs to cluster 9d2530c104. The cluster view shows all associated addresses, including several labelled CoinJoinMess — WalletExplorer’s annotation for addresses associated with CoinJoin mixing transactions, part of the obfuscation layer used in the laundering operation.
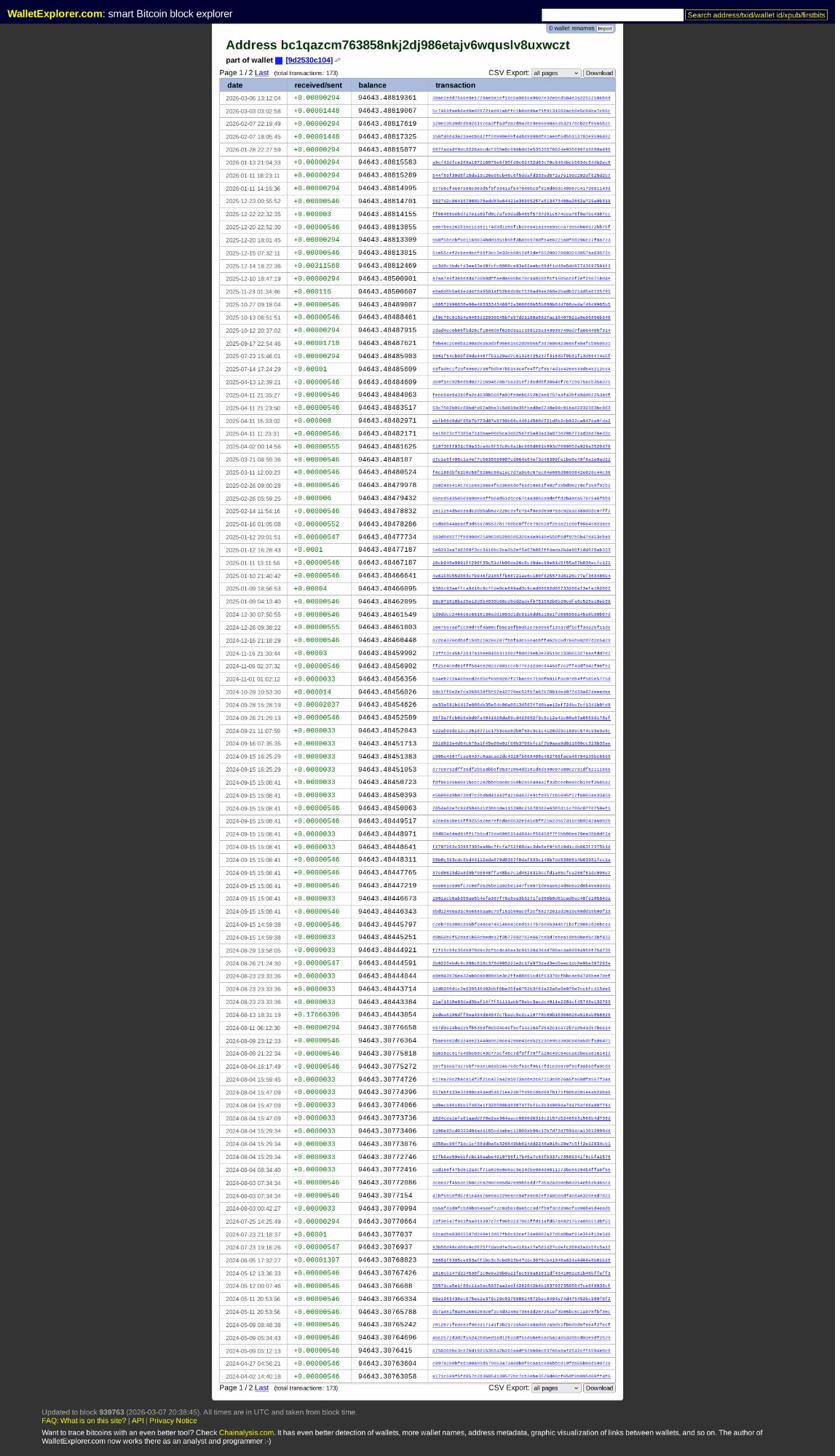
9d2530c104. 173 transactions. CSV export available. The footer states: “The author of WalletExplorer.com now works there as an analyst and programmer” — linking directly to Chainalysis.com.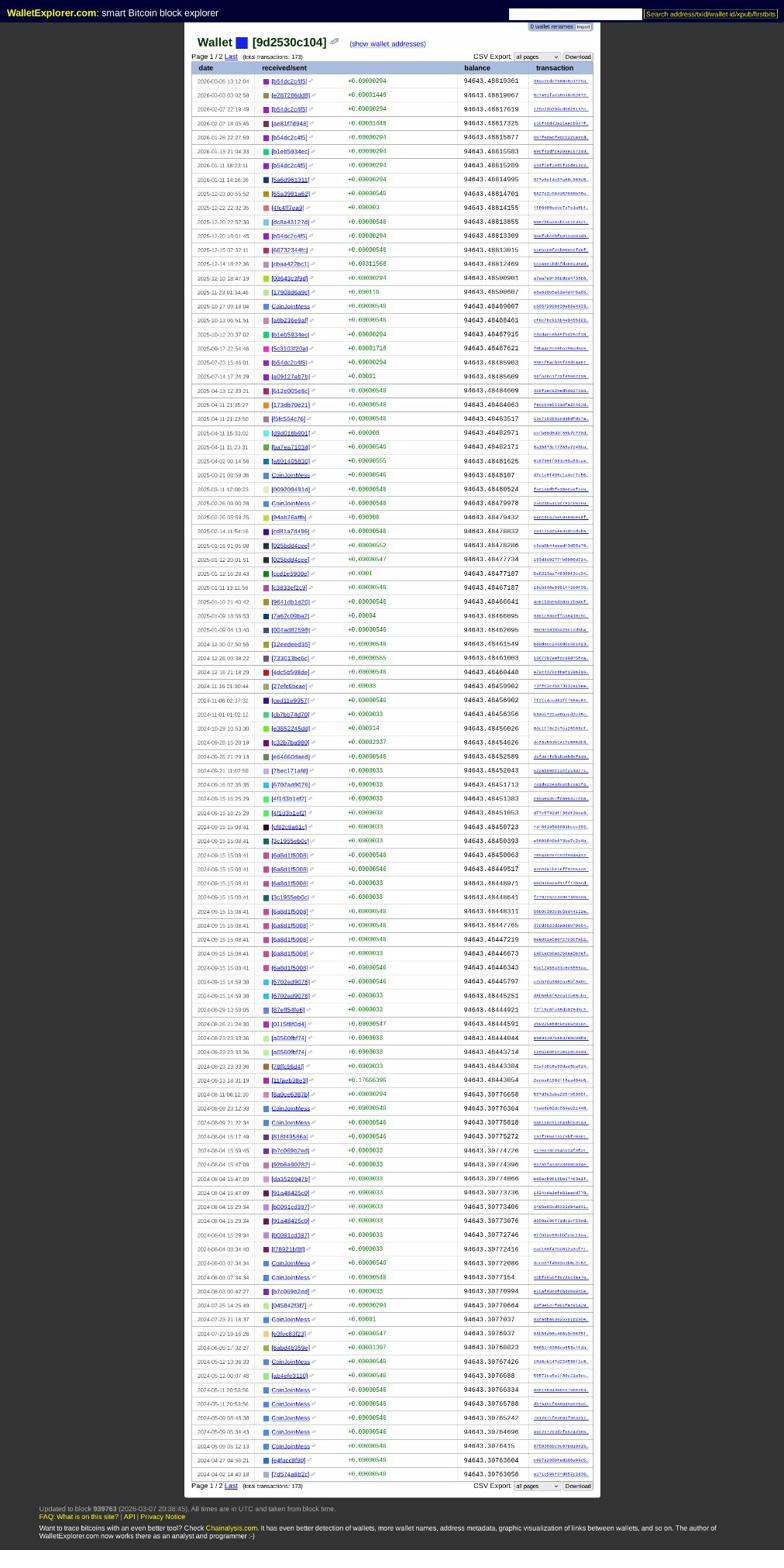
9d2530c104. All addresses associated with the FBI3 custody wallet. Several sending addresses carry the CoinJoinMess label — the mixing layer that preceded the seizure, still visible in the cluster record.The operational consideration is what happens to the lookup itself. WalletExplorer’s creator now works at Chainalysis — the dominant blockchain intelligence firm under contract with the FBI, IRS Criminal Investigation, DEA, and Europol. Using WalletExplorer on clearnet logs your IP against the address you queried. That log sits with an entity whose commercial purpose is providing investigative data to law enforcement.
The lookups for this investigation were conducted via WalletExplorer’s Tor hidden service.
Following the transaction chain
The consolidation on February 1, 2022 began at 04:14 UTC with a single 1 BTC test, then proceeded in scripted batches. Transaction afdfeeadb9f0 — the first major sweep at 04:27 UTC — moved 10,000 BTC from 223 input addresses into the FBI3 wallet. Fee: 0.00420162 BTC. Roughly $160 to move approximately $400 million.
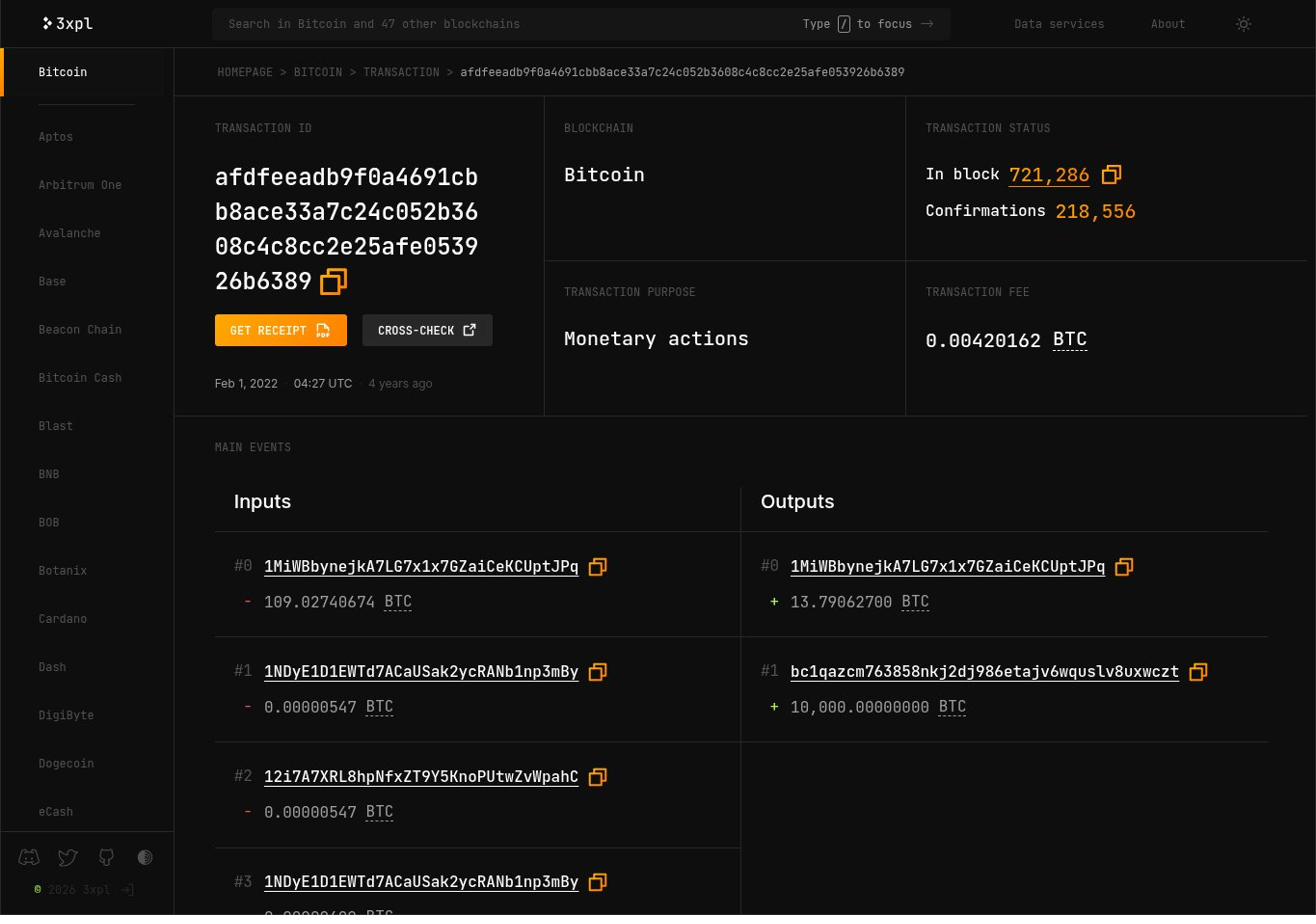
1MiWBbynejkA7LG7x1x7GZaiCeKCUptJPq. Block 721,286.The change output — 13.79062700 BTC to 1MiWBbynejkA7LG7x1x7GZaiCeKCUptJPq — is the remainder from the sweep, returned to a staging address for collection in the next pass 84 minutes later. Looking up that address returns its complete transaction history on a single screen.
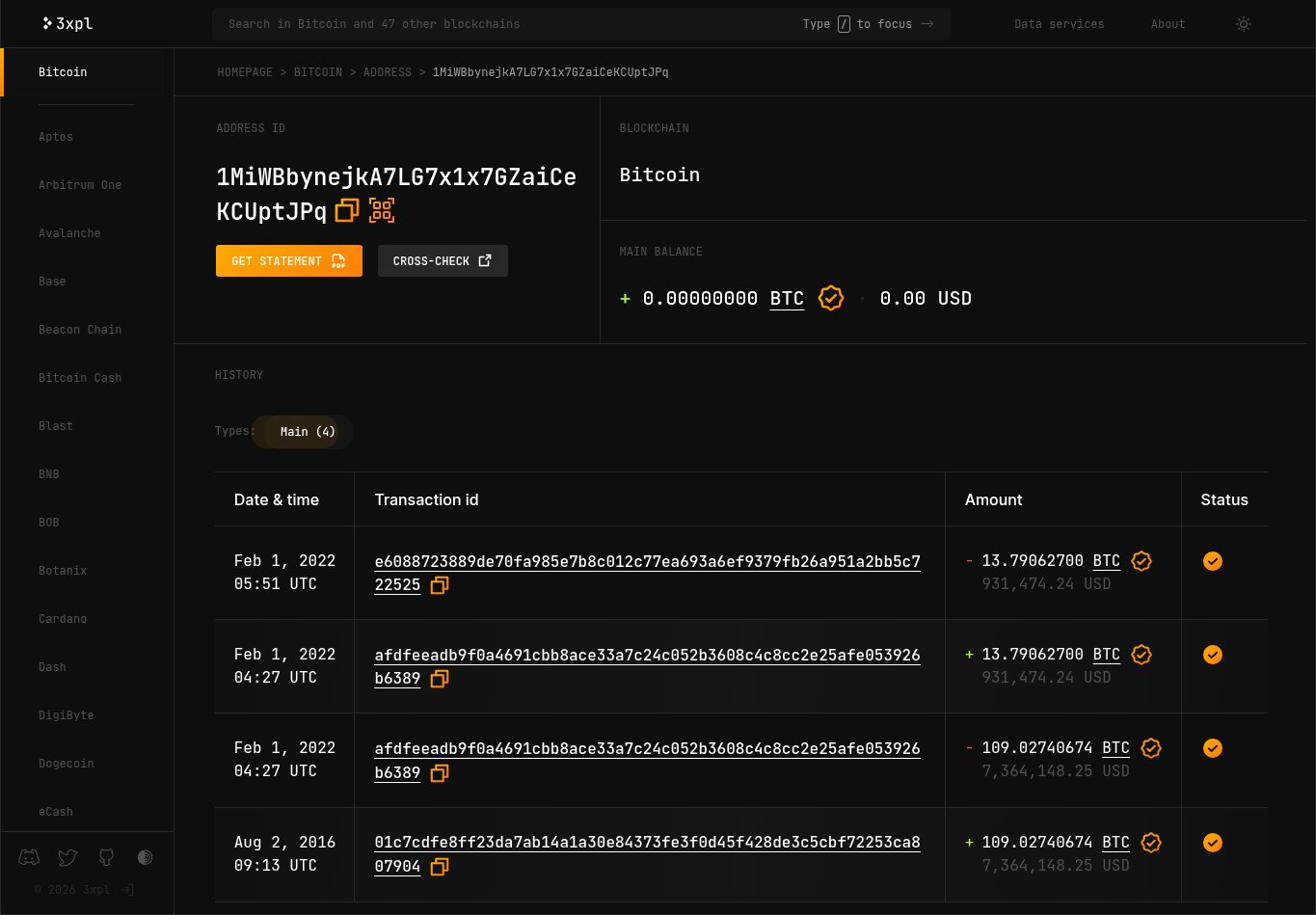
1MiWBbynejkA7LG7x1x7GZaiCeKCUptJPq. Four transactions. Received 109.02740674 BTC on Aug 2, 2016. Spent across two transactions on Feb 1, 2022. Balance: zero. The address was active for a single morning in 2016, then dormant for 2,009 days.The first transaction on that address links to transaction 01c7cdfe8ff2 — dated August 2, 2016, 09:13 UTC. The date of the Bitfinex hack.
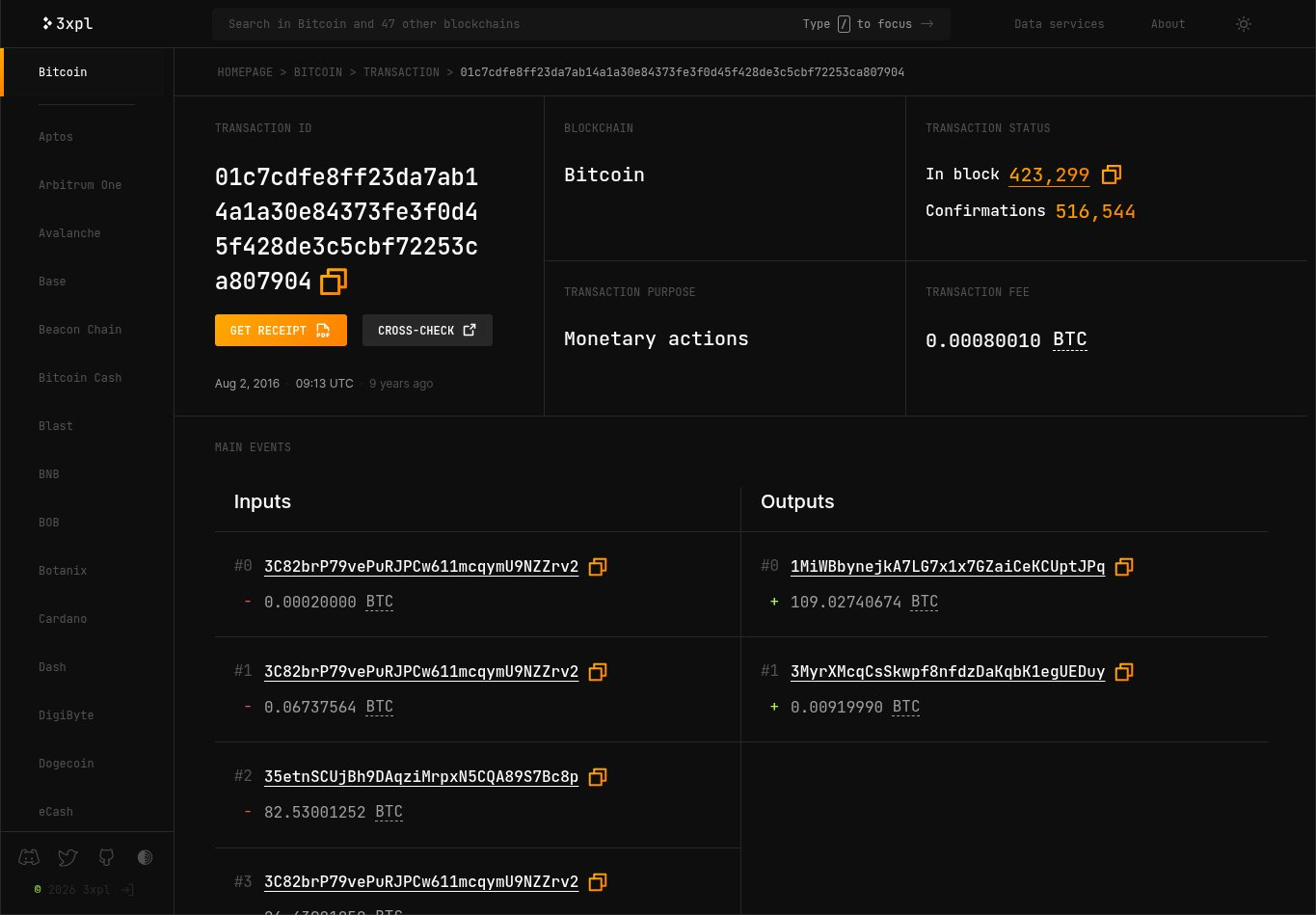
01c7cdfe8ff2. August 2, 2016, 09:13 UTC. Inputs include 35etnSCUjBh9DAqziMrpxN5CQA89S7Bc8p contributing 82.53 BTC and 3C82brP79vePuRJPCw611mcqymU9NZZrv2 — the Bitfinex hot wallet. Output: 109.02740674 BTC to 1MiWBbynejkA7LG7x1x7GZaiCeKCUptJPq. This is the theft transaction.One of the inputs — 35etnSCUjBh9DAqziMrpxN5CQA89S7Bc8p — spent 82.53001252 BTC into that transaction. Looking it up shows a two-transaction address with a zero balance. Its entire history fits in four rows.
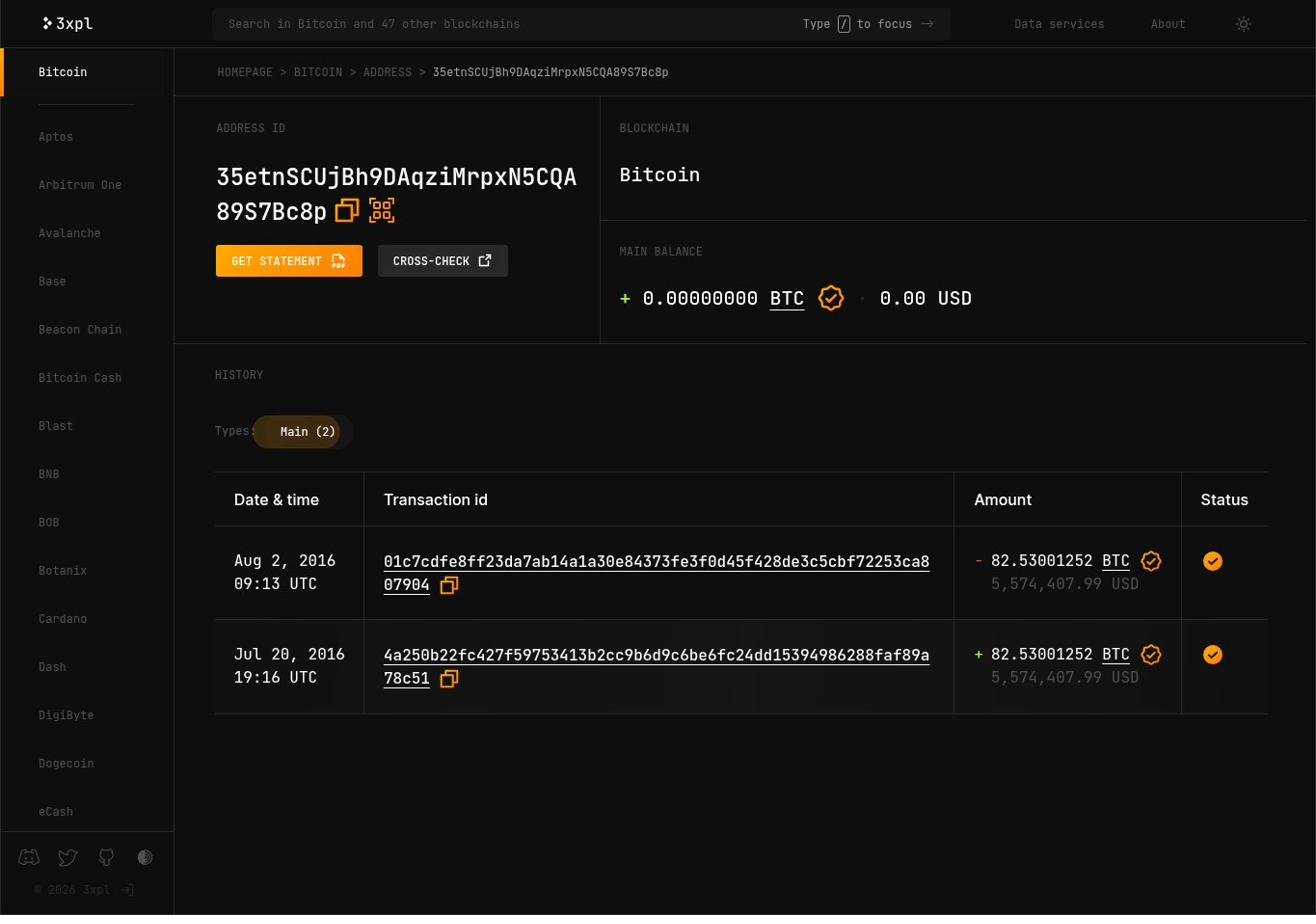
35etnSCUjBh9DAqziMrpxN5CQA89S7Bc8p. Received 82.53001252 BTC on July 20, 2016. Spent in full on August 2, 2016 — the day of the hack. Two transactions, zero balance, never used again.This address was funded on July 20, 2016 — 13 days before the theft. The funding transaction, 4a250b22fc42, shows the source: 3C82brP79vePuRJPCw611mcqymU9NZZrv2, the same Bitfinex hot wallet address that appears as an input in the hack transaction itself.
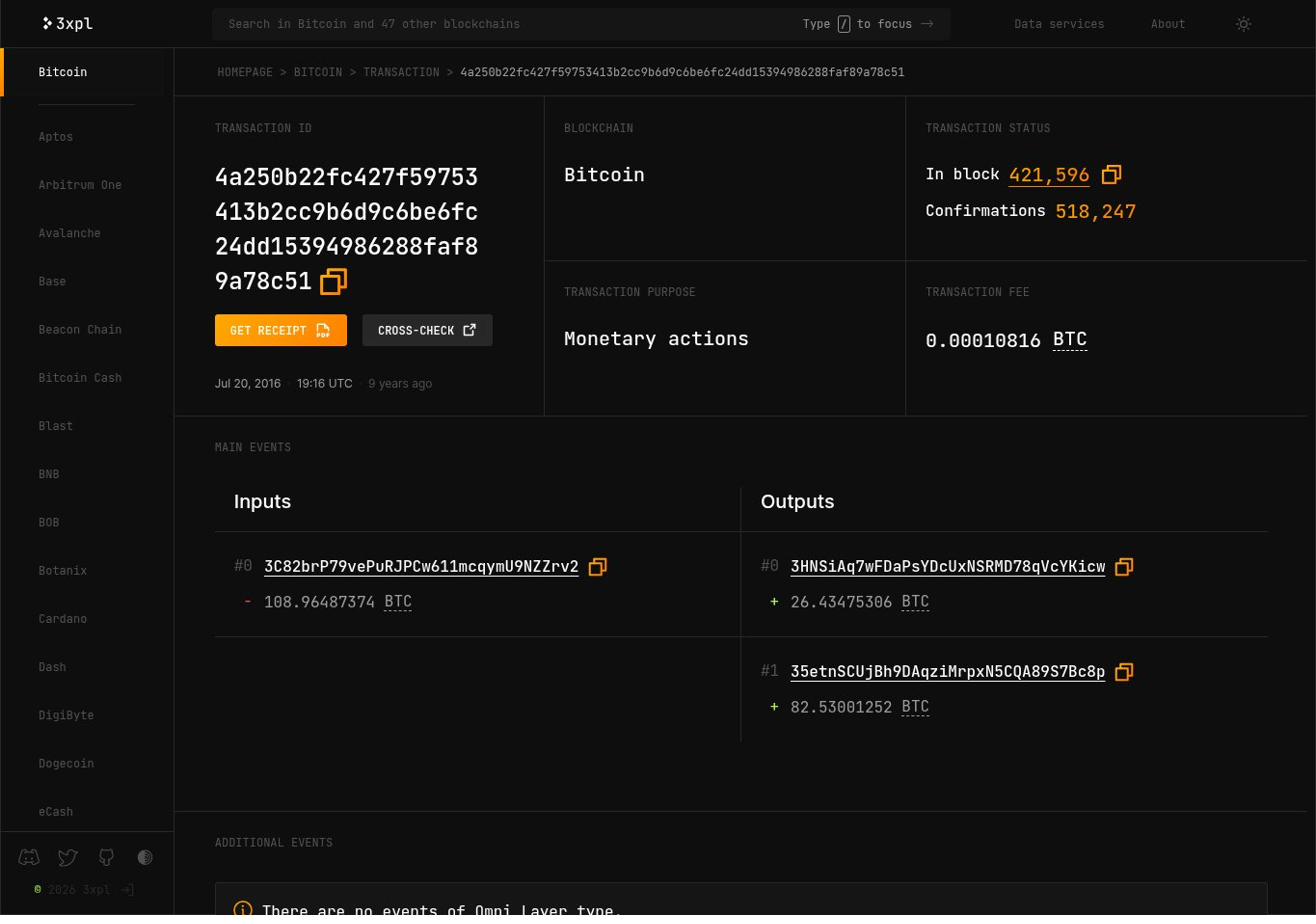
4a250b22fc42. July 20, 2016, 19:16 UTC. Input: 3C82brP79vePuRJPCw611mcqymU9NZZrv2 spending 108.96 BTC. Output: 82.53001252 BTC to 35etnSCUjBh9DAqziMrpxN5CQA89S7Bc8p. The attack infrastructure was funded from Bitfinex’s own hot wallet 13 days before the theft executed.The full chain, reconstructed from public data:
3C82brP79ve funds staging address 35etn… with +82.53 BTC. Attack infrastructure pre-positioned 13 days before the theft.
3C82brP79ve spend together. Output: +109.02740674 BTC to staging address 1MiWBb…. This is the theft transaction.
The staging address 35etn was funded from Bitfinex’s own hot wallet 13 days before the hack. The attacker had access to move funds out of the exchange before the theft executed. The public record has contained this detail since August 2, 2016. Finding it required following two transactions back from the seizure.
The consolidation
The full February 1 sweep comprised 22 transactions across 133 minutes. A test transaction at 04:14, then batches of increasing size in parallel, ending with a dust pass collecting fractional remainders from 510 addresses simultaneously.
The FBI did not crack Lichtenstein’s encryption. They found the keys — stored in an encrypted file on cloud storage that agents accessed. The six-year laundering operation held technically. The storage decision did not.
The dust record
The FBI3 wallet received 153 transactions after the consolidation. Every one is under 0.001 BTC. These are analyst tracking tags — small amounts sent to anchor an address in a monitoring system, or to associate it with a researcher’s own address for later graph analysis. The first arrived on February 2, 2022, one day after the seizure. The community was watching before the arrests were announced on February 8.
During this investigation, the most recent transaction on the 3xpl address page — Mar 8, 2026, 00:51 UTC, +0.00000294 BTC, $0.19 — arrived while the lookup was running. The wallet is watched continuously. The blockchain does not distinguish between who is watching.
What the trace demonstrates
Starting from the FBI3 custody wallet, two hops back through the transaction graph reached a staging address funded from Bitfinex’s own hot wallet on July 20, 2016 — 13 days before the theft. The entire chain is in the public record. It was always there. Finding it required choosing the right tool and following the transactions.
This is what blockchain transparency means in practice. The data is permanent and complete. The variable is the analytical layer: which tools surface it, whether the addresses carry labels, and what those tools do with the fact that you queried them. The same address across four tools returned four different experiences of the same public record.
The methodology that broke the case was not purely the blockchain component. Lichtenstein’s laundering held technically for six years. What collapsed it was the intersection of digital behaviour with ordinary commercial infrastructure: an encrypted file in cloud storage found by agents with account access. And separately — Heather Morgan redeeming a Walmart gift card with her real name, linked to a loyalty programme, linked to a darknet forum registration, linked to a cryptocurrency address. $9.4 billion concealed across 2,009 days. Ended by a receipt.
The same cross-referencing approach — loyalty programme records, commercial transaction data, corporate registry filings, data broker profiles — is what a personal exposure audit runs against a name. The blockchain is one axis. It is rarely the only one.